There’s no denying that cloud storage offers unparalleled convenience. However, can it secure protected health information and maintain HIPAA compliance?
The Health Insurance Portability and Accountability Act has specific obligations for cloud storage providers who handle healthcare data. These requirements are essential for protecting sensitive information and closely align with those applicable to on-premise storage systems.
Whether you are a healthcare professional, an IT administrator, or a compliance officer, this article will give you a comprehensive overview of the requirements for HIPAA-compliant cloud storage.
Can HIPAA Data Be Stored in the Cloud?
HIPAA does not prohibit healthcare organizations from storing PHI in the cloud. However, it mandates specific privacy and security safeguards to guarantee the confidentiality, integrity, and availability of electronic PHI (ePHI). These requirements ensure that healthcare organizations can securely leverage cloud storage while protecting patient privacy.
Despite the term “cloud” often being associated with something intangible and transient, cloud computing relies on physical servers. Subsequently, all HIPAA security requirements apply equally to cloud, hybrid cloud, or on-premise data storage systems.
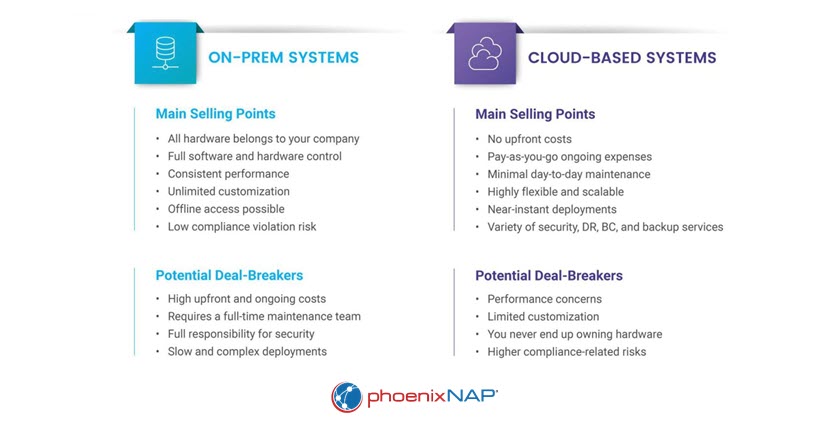
Not quite sure what solution is better for your organization? Read about the differences between on-premises vs. cloud computing on our blog.
What Are HIPAA Requirements for Cloud Storage?
HIPAA-compliant cloud storage providers (CSPs) must adhere to rigorous controls stipulated by the HIPAA Privacy and Security Rules. These regulations require administrative, physical, and technical safeguards to ensure that sensitive data is consistently protected. Additionally, the HIPAA Breach Notification Rule mandates that the CSP promptly notify the covered entity or business associate in case of a PHI breach.
Here are the requirements for HIPAA-compliant cloud storage:
1. Robust Access Controls
HIPAA-compliant cloud storage solutions must have strong controls to restrict unauthorized access to electronic protected health information (ePHI). Examples of safeguards include multifactor authentication, role-based access control, and end-to-end encryption.
Zero trust security fundamentally transforms access controls by shifting from a perimeter-based approach to a model that verifies and authenticates every user and device attempting to access resources, regardless of their location or network.
2. Event Logging and Audit Trails
CSPs must maintain comprehensive event logs that capture and document all system activity. These logs serve as an audit trail, enabling internal or external auditors to track access, modifications, and other actions related to ePHI.
The availability of detailed audit trails also helps with investigating data breaches and conducting vulnerability assessments.
3. Regular Risk Assessments
CSPs must conduct frequent risk assessments and thorough evaluations of their platform’s security. A proactive risk management strategy identifies weaknesses and allows for timely remediation. Regular reviews also ensure that the storage environment complies with constantly evolving regulations.
4. High Uptime and Availability
Healthcare organizations need continuous access to patient data, as any disruption or downtime can impact patient care and violate HIPAA. Therefore, high-availability cloud solutions are essential for storing ePHI.
CSPs must have robust infrastructure, redundancy measures, and business continuity and disaster recovery protocols to maintain the uninterrupted availability of ePHI.
5. Robust Backup Strategy
HIPAA-compliant CSPs must have a strong backup strategy to prevent data loss. This strategy enables information recovery in case of accidental deletion, system failures, cyber-attacks, or natural disasters. CSPs must also regularly test their plan to validate its effectiveness and ability to restore data accurately.
Business Associate Agreements
Under HIPAA, when a covered entity or its business associate engages a CSP to process or store ePHI, the CSP assumes the role of business associate. Subsequently, the covered entity and the CSP must establish a HIPAA-compliant business associate agreement (BAA) to govern their relationship.
The BAA outlines the legal obligations of the CSP and ensures they are aware of their responsibility to protect ePHI. Even in cases where a CSP only processes or stores ePHI without having access to the encryption key, they are still subject to business associate status.
Furthermore, as a business associate, the CSP assumes direct liability if they fail to store ePHI adequately. HIPAA’s governing body, The Department of Health and Human Services Office for Civil Rights (OCR), conducts HIPAA compliance audits as a primary control mechanism.
The OCR might issue fines and penalties if they determine the CSP caused a HIPAA violation due to malice or willful neglect.
phoenixNAP’s Data Security Cloud offers a fully HIPAA-compliant cloud solution for organizations of all sizes. We partnered with Intel, VMWare, Sophos and Alert Logic to build the most secure cloud infrastructure platform.
How to Choose HIPAA-Compliant Cloud Storage?
Selecting the right cloud storage solution requires careful consideration. Here are the key factors for choosing a HIPAA-compliant cloud storage provider:
- Third-Party Accreditation: Look for CSPs that are accredited by reputable third-party compliance firms. The accreditation demonstrates a commitment to HIPAA compliance and data security.
- Service Level Agreement (SLA): Prioritize providers that offer service level agreements that guarantee excellent performance and near 100% uptime. A good SLA ensures uninterrupted access to critical information, minimizing disruptions and delays.
- Encryption Measures: Verify that the provider has strong measures for data encryption at rest and data encryption in transit, aligning with the cryptographic standards recommended by the National Institute of Standards and Technology. Comprehensive encryption ensures that sensitive data remains protected from unauthorized access throughout its lifecycle.
- Disaster Recovery Services: Evaluate the provider’s disaster recovery as a service offering, including data backup and offsite storage capabilities. A comprehensive and well-defined disaster recovery plan ensures business continuity and minimizes data loss in case of a disaster or system failure.
- Breach Notification Response: The sooner you are notified, the faster you can respond to a data breach. Inquire about the provider’s breach notification response times and protocols.
- Physical Security: To ensure the protection of your data, assess the physical security of the provider’s data centers. Look for features such as access control systems, surveillance cameras, environmental controls, and perimeter security.

Our HIPAA-compliant hosting is secure by design and constructed to meet the rigorous privacy requirements of the healthcare industry. With strong encryption measures, stringent access controls, and comprehensive data backup and recovery capabilities, we offer unparalleled protection of sensitive health information.
Conclusion
HIPAA allows covered entities and business associates to use cloud storage for protected health information. The standards for safeguarding electronic PHI in the cloud are as stringent as those for on-premises systems.
When selecting a cloud provider for storing ePHI, it is crucial to ensure they possess the capabilities and expertise necessary to meet HIPAA mandates. Establishing a Business Associate Agreement (BAA) with the cloud provider binds the provider to adhere to the same high ePHI protection standards as the covered entity or business associate.
By selecting a reliable and capable cloud provider and entering a BAA, healthcare organizations can maintain HIPAA compliance while leveraging the benefits of the cloud.



