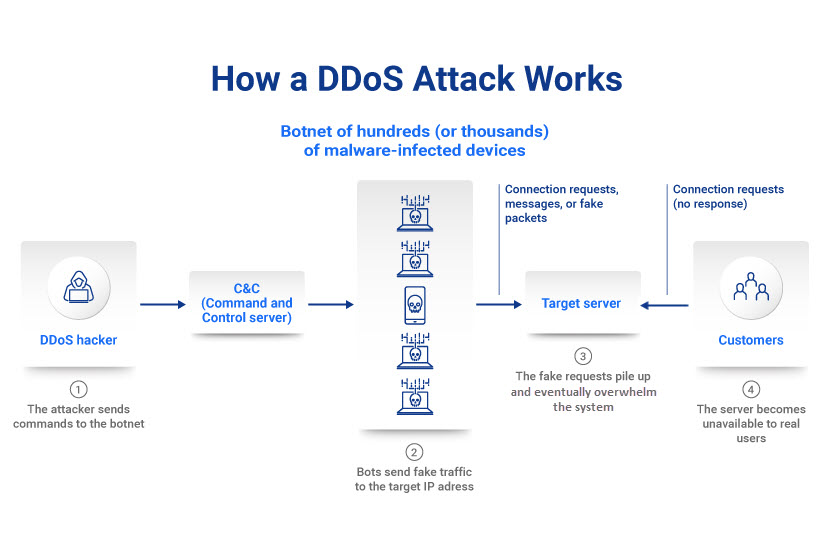
A DDoS attack enables a hacker to flood a network or server with bogus traffic. Too much traffic overloads resources and disrupts connectivity, stopping the system from processing genuine user requests. Services become unavailable, and the target company suffers prolonged downtime, lost revenue, and dissatisfied customers.
This article explains how a business can prevent DDoS attacks and stay a step ahead of would-be hackers. The practices we show below help minimize the impact of a DDoS and ensure a quick recovery from an attack attempt.
What Is a DDoS Attack?
A DDoS (Distributed Denial of Service) is a cyberattack that aims to crash a network, service, or server by flooding the system with fake traffic. The sudden spike in messages, connection requests, or packets overwhelms the target's infrastructure and causes the system to slow down or crash.
While some hackers use DDoS attacks to blackmail a business into paying a ransom (similar to ransomware), more common motives behind a DDoS are to:
- Disrupt services or communications.
- Inflict brand damage.
- Gain a business advantage while a competitor's website is down.
- Distract the incident response team.
DDoS attacks are a danger to businesses of all sizes, from Fortune 500 companies to small e-retailers. Statistically, DDoS hackers most often target:
- Online retailers.
- IT service providers.
- Financial and fintech companies.
- Government entities.
- Online gaming and gambling companies.
Attackers typically use a botnet to cause a DDoS. A botnet is a linked network of malware-infected computers, mobile devices, and IoT gadgets under the attacker's control. Hackers use these "zombie" devices to send excessive numbers of requests to a target website or server's IP address.
Once the botnet sends enough requests, online services (emails, websites, web apps, etc.) slow down or fail. According to a Radware report, these are the average lengths of a DDoS attack:
- 33% keep services unavailable for an hour.
- 60% last less than a full day.
- 15% last for a month.
While a DDoS typically does not directly lead to a data breach or leakage, the victim spends time and money getting services back online. Loss of business, abandoned shopping carts, frustrated users, and reputational harm are usual consequences of failing to prevent DDoS attacks.
A DDoS is often a distraction for other, more disastrous threats. Read about the most dangerous cyber security attack types and learn how to protect your business.
Types of DDoS Attacks
While all DDoS attacks aim to overwhelm a system with too much activity, hackers have different strategies they rely on to cause a distributed denial of service.
The three main types of attack are:
- Application-layer attacks.
- Protocol attacks.
- Volumetric attacks.
The three approaches rely on different techniques, but a skilled hacker can employ all three strategies to overwhelm a single target.
All pNAP servers come with DDoS protection at no additional cost. Stay online 24/7 with our automated traffic filtering and lightning-fast DDoS mitigation infrastructure.
Application-Layer Attacks
An application-layer attack targets and disrupts a specific app, not an entire network. A hacker generates a high number of HTTP requests that exhaust the target server's ability to respond.
Cybersecurity specialists measure app-layer attacks in requests per second (RPS). Common targets of these attacks include:
- Web apps.
- Internet-connected apps.
- Cloud services.
Trying to prevent DDoS attacks of this type is challenging as security teams often struggle to distinguish between legitimate and malicious HTTP requests. These attacks use fewer resources than other DDoS strategies, and some hackers can even use only a single device to orchestrate an application-layer attack.
Another common name for an app-level DDoS is a layer 7 attack.
Protocol Attacks
Protocol DDoS attacks (or network-layer attacks) exploit weaknesses in the protocols or procedures that govern internet communications. While an app-level DDoS targets a specific app, the goal of a protocol attack is to slow down the entire network.
The two most common types of protocol-based DDoS attacks are:
- SYN floods: This attack exploits the TCP handshake procedure. An attacker sends TCP requests with fake IP addresses to the target. The target system responds and waits for the sender to confirm the handshake. As the attacker never sends the response to complete the handshake, the incomplete processes pile up and eventually crash the server.
- Smurf DDoS: A hacker uses malware to create a network packet attached to a false IP address (spoofing). The package contains an ICMP ping message that asks the network to send back a reply. The hacker sends the responses (echos) back to the network IP address again, creating an infinite loop that eventually crashes the system.
Cybersecurity experts measure protocol attacks in packets per second (PPS) or bits per second (BPS). The main reason why protocol DDoS is so widespread is that these attacks can easily bypass poorly configured firewalls.
Volumetric Attacks
A volume-based DDoS attack consumes a target's available bandwidth with false data requests and creates network congestion. The attacker's traffic blocks legitimate users from accessing services, preventing traffic from flowing in or out.
The most common types of volumetric DDoS attack types are:
- UDP floods: These attacks allow a hacker to overwhelm ports on the target host with IP packets containing the stateless UDP protocol.
- DNS amplification (or DNS reflection): This attack redirects high amounts of DNS requests to the target's IP address.
- ICMP flood: This strategy uses ICMP false error requests to overload the network's bandwidth.
All volumetric attacks rely on botnets. Hackers use armies of malware-infected devices to cause traffic spikes and use up all available bandwidth. Volumetric attacks are the most common type of DDoS.
Bare Metal Cloud, pNAP's cloud-native dedicated server, offers a robust resistance to DDoS. Each server comes with free 20 Gbps DDoS protection that ensures availability even if you face a high-traffic volumetric attack.
7 Best Practices to Prevent DDoS Attacks
While there is no way to prevent a hacker from attempting to cause a DDoS, proper planning and proactive measures reduce the risk and potential impact of an attack.

Create a DDoS Response Plan
Your security team should develop an incident response plan that ensures staff members respond promptly and effectively in case of a DDoS. This plan should cover:
- Clear, step-by-step instructions on how to react to a DDoS attack.
- How to maintain business operations.
- Go-to staff members and key stakeholders.
- Escalation protocols.
- Team responsibilities.
- A checklist of all necessary tools.
- A list of mission-critical systems.
The ability to react to unexpected events is vital to business continuity. Our article on disaster recovery takes you through all you need to know to create an effective DR plan.
Ensure High Levels of Network Security
Network security is essential for stopping any DDoS attack attempt. As an attack only has an impact if a hacker has enough time to pile up requests, the ability to identify a DDoS early on is vital to controlling the blast radius.
You can rely on the following types of network security to protect your business from DDoS attempts:
- Firewalls and intrusion detection systems that act as traffic-scanning barriers between networks.
- Anti-virus and anti-malware software that detects and removes viruses and malware.
- Endpoint security that ensures network endpoints (desktops, laptops, mobile devices, etc.) do not become an entry point for malicious activity.
- Web security tools that remove web-based threats, block abnormal traffic, and search for known attack signatures.
- Tools that prevent spoofing by checking if traffic has a source address consistent with the origin addresses.
- Network segmentation that separates systems into subnets with unqiue security controls and protocols.
Protecting from DDoS attacks also requires high levels of network infrastructure security. Securing networking devices enables you to prepare your hardware (routers, load-balancers, Domain Name Systems (DNS), etc.) for traffic spikes.
A vulnerability assessment enables you to identify weaknesses in your network before a hacker does. For an even more in-depth analysis, you can also run a penetration test.
Have Server Redundancy
Relying on multiple distributed servers makes it hard for a hacker to attack all servers at the same time. If an attacker launches a successful DDoS on a single hosting device, other servers remain unaffected and take on extra traffic until the targeted system is back online.
You should host servers at data centers and colocation facilities in different regions to ensure you do not have any network bottlenecks or single points of failure. You can also use a content delivery network (CDN). Since DDoS attacks work by overloading a server, a CDN can share the load equally across several distributed servers.
PhoenixNAP's colocation services enable you to set up an optimal hosting environment while enjoying top levels of security, high redundancy, and a variety of managed services.
Look Out for the Warning Signs
If your security team can quickly identify the traits of a DDoS attack, you can take timely action and mitigate the damage.
Common signs of a DDoS are:
- Poor connectivity.
- Slow performance.
- High demand for a single page or endpoint.
- Crashes.
- Unusual traffic coming from a single or a small group of IP addresses.
- A spike in traffic from users with a common profile (system model, geolocation, web browser version, etc.).
Remember that not all DDoS attacks come with high traffic. A low-volume attack with a short duration often goes under the radar as a random event. However, these attacks can be a test or diversion for a more dangerous breach (such as ransomware). Therefore, detecting a low-volume attack is as vital as identifying a full-blown DDoS.
Consider organizing a security awareness training program that educates the entire staff on the signs of a DDoS attack. That way, you do not need to wait for a security team member to pick up on the warning signs.

Continuous Monitoring of Network Traffic
Using continuous monitoring (CM) to analyze traffic in real-time is an excellent method of detecting traces of DDoS activity. The benefits of CM are:
- Real-time monitoring ensures you detect a DDoS attempt before the attack takes full swing.
- The team can establish a strong sense of typical network activity and traffic patterns. Once you know how everyday operations look, the team easier identifies odd activities.
- Around-the-clock monitoring ensures the detection of signs of an attack that happens outside of office hours and on weekends.
Depending on a setup, the CM tool either contacts admins in case of an issue or follow response instructions from a pre-defined script.
Intrigued by continuous monitoring? Our Nagios tutorial explores this popular CM tool and offers an ideal starting point for newcomers to Nagios.
Limit Network Broadcasting
A hacker behind a DDoS attack will likely send requests to every device on your network to amplify the impact. Your security team can counter this tactic by limiting network broadcasting between devices.
Limiting (or, where possible, turning off) broadcast forwarding is an effective way to disrupt a high-volume DDoS attempt. Where possible, you can also consider instructing employees to disable echo and chargen services.
Learn how to check and mitigate a DDoS attack on Linux server.
Leverage the Cloud to Prevent DDoS Attacks
While using on-prem hardware and software to counter the DDoS threat is vital, cloud-based mitigation does not have the same capacity limitations. Cloud-based protection can scale and handle even a major volumetric DDoS attack with ease.
You have the option of outsourcing DDoS prevention to a cloud provider. Some of the key benefits of working with a third-party vendor are:
- Cloud providers offer well-rounded cybersecurity, with top firewalls and threat monitoring software.
- The public cloud has greater bandwidth than any private network.
- Data centers provide high network redundancy with copies of data, systems, and equipment.
A business typically has two choices when setting up cloud-based DDoS protection:
- On-demand cloud DDoS mitigation: These services activate after the in-house team or the provider detects a threat. If you suffer a DDoS, the provider diverts all traffic to cloud resources to keep services online.
- Always-on cloud DDoS protection: These services route all traffic through a cloud scrubbing center (at the cost of minor latency). This option is best suited for mission-critical apps that cannot afford downtime.
If your in-house team has the necessary know-how, you may not need to solely rely on a cloud provider for cloud-based DDoS protection. You can set up a hybrid or multi-cloud environment and organize your traffic to get the same effects as either on-demand or always-on DDoS protection.
Learn about the most recent data breaches by refering to our article Data Breach Statistics.
Do Not Overlook the DDoS Threat
DDoS threats are not only becoming more dangerous, but attacks are also increasing in number. Experts predict the average number of annual DDoS attempts will rise to 15.4 million by 2023. That number indicates that nearly every business will face a DDoS at some point, so preparing for this attack type should be at the top of your security to-do list.